Software developers have a supply chain security problem
Log4j was the bucket of cold drinking water that woke up most developers to their software package offer chain safety problem.
We’ve spent decades in software package developing factors and obsessing more than our output ecosystem. But we’re building on unpatched Jenkins packing containers sitting under someone’s desk. We shell out all this time defending our runtimes, then deploy to them employing amateur tooling.
Our build environments aren’t just about as protected as our production environments.
That’s what led to a whole whole lot of high-profile attacks in the final 12 months, from SolarWinds, to the Codecov assault, to the Travis CI techniques leak. We have gotten so good at protecting our infrastructure that attackers appeared for an less difficult way in, and found it in the doorways we have left open in the offer chain.
Can’t get in through the perimeter protection? Just locate an open up source dependency, or a library, and get in that way. Then pivot to all of the shoppers. This is the contemporary software offer chain hack.
We want roots of rely on for computer software
We have roots of trust for men and women nowadays. We have two-issue authentication, we have identification programs. These are factors to vouch for a person’s identity. And components has the identical point. We have encryption keys. We have components we can have confidence in hasn’t been tampered with when it boots up.
Even as world-wide-web consumers we have roots of trust. We have URIs, URNs, and URLs—effectively the namespaces on the world wide web that hook up the identities, names, and locations of web-sites we are browsing. SSL certificates inform our browsers that sites are protected. DNS firewalls sit amongst the user’s recursive resolvers to make certain our cache is not getting loaded with lousy requests. All of this is taking place behind the scenes, and has been very powerful in supporting billions of world-wide-web customers for many years.
But we don’t have this for application artifacts now.
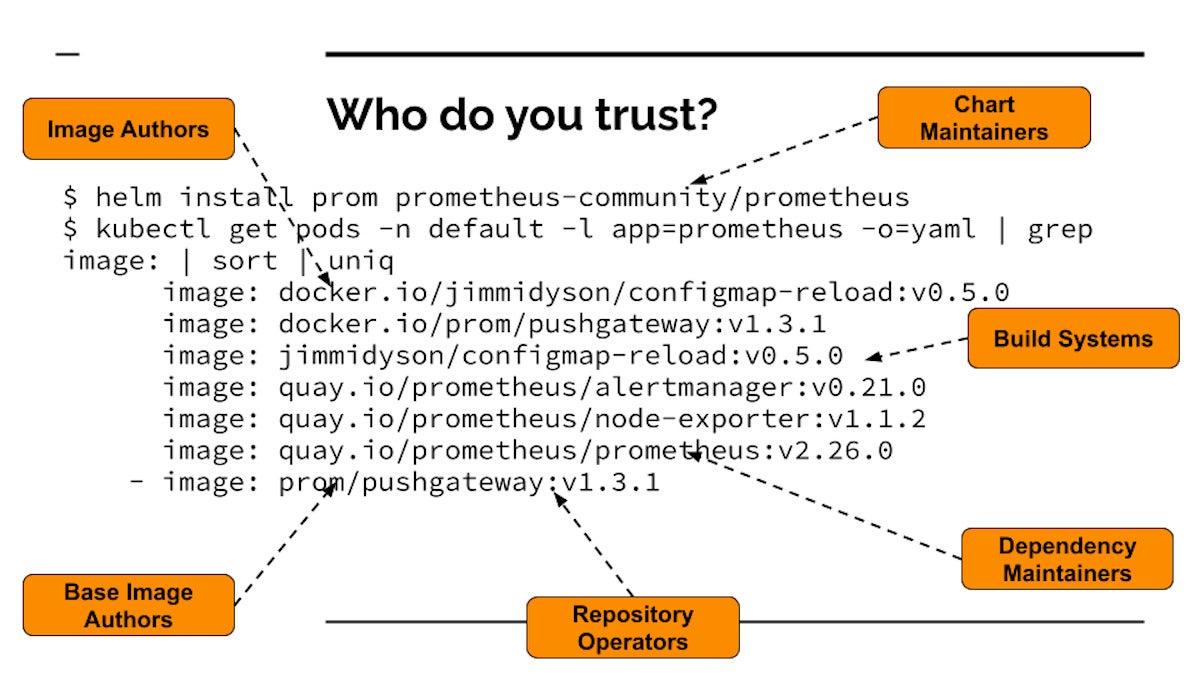
Builders rely on much too considerably implicitly
Consider an party as commonplace as putting in Prometheus (a well-liked open up resource observability challenge) from the Cloud Indigenous Computing Basis (CNCF) artifact hub. If you do your Helm put in and then seem at all the pictures that get pulled and start out running your cluster, you see many container visuals that finish up jogging from a basic set up. Developers are entrusting a full bunch of factors to a full bunch of different folks and methods. Each individual single a person of these could be tampered with or attacked, or could be malicious.
 Dan Lorenc
Dan LorencThis is the opposite of Zero Trust—we’re trusting dozens of methods that we do not know anything about. We don’t know the authors, we really don’t know if the code is destructive, and simply because each and every image has its very own artifacts, the full supply chain is recursive. So we’re not only trusting the artifacts, but also the persons who trustworthy the dependencies of these artifacts.
We’re also trusting the persons who operate the repositories. So if the repository operators get compromised, now the compromisers are section of your believe in circle. Anybody controlling a single of these repositories could change a thing and attack you.
Then there’s the build units. Construct systems can get attacked and insert malicious code. Which is precisely what occurred with SolarWinds. Even if you know and trust the operators of the photographs, and the people today running the methods that host the images, if these are designed insecurely, then some malware can get inserted. And again it is recursive all the way down. The dependency maintainers, the make programs they use, the artifact administrators that they are hosted on—they’re all undermined.
So when builders put in computer software deals, there are a good deal of matters they are trusting implicitly, whether they signify to belief them or not.
Program source chain protection gotchas
The worst system you can have in software provide chain security is to do practically nothing, which is what a ton of developers are executing today. They are allowing for something to run on output environments. If you have no stability all-around what artifacts can run, then you have no notion wherever they arrived from. This is the worst of the worst. This is not shelling out awareness at all.
Make it possible for-listing distinct tags is the up coming level up. If you go as a result of some of the tutorials around greatest methods with Kubernetes, this is very easy to set up. If you press all your visuals to a single place, you can at the very least prohibit factors to that spot. That’s way far better than performing nothing at all, but it’s nonetheless not wonderful, since then anything at all that will get pushed there is now within your have confidence in circle, within that barbed wire fence, and that is not actually Zero Have faith in. Enable-listing distinct repositories has all the exact same restrictions of allow-listing unique tags.
Even the signing schemas in source chain stability are papering more than the exact difficulty. Something that gets signed now gets to operate, no matter of where by it arrived from, which qualified prospects to tons of assaults tied to tricking an individual to indication the improper point, or remaining not able to revoke a certification.
Time to begin inquiring the proper issues
Let us say you’re going for walks down the sidewalk exterior of your business, and you come across a USB thumb generate sitting on the floor. I hope anyone appreciates that you need to definitely not acquire that push within your office environment and plug it into your workstation. Everybody in application must (rightly) be screaming, “No!” Real attacks have took place this way, and security orgs across the globe hammer this warning into all personnel as section of coaching.
But for some rationale, we don’t even pause to imagine two times just before functioning docker pull or npm set up, even nevertheless these are arguably even worse than plugging in a random USB stick. Each cases include getting code from somebody you do not have confidence in and operating it, but the Docker container or NPM package will at some point make it all the way into your creation natural environment!
The essence of this source chain protection evolution is that as an field we’re going away from trusting the place the software artifacts occur from, and paying substantially a lot more time figuring out roots of rely on for what the artifact is.
Who released this binary? How was it crafted? What model of the device was used? What supply was it constructed from? Who signed off on this code? Was everything tampered with? These are the proper issues to be asking.
Upcoming week, we’ll glance at the quick-evolving open up resource landscape that is forming a new protection stack for provide chain stability, and unpack important principles builders require to understand—from roots of belief, to provenance, to TPM (Trustworthy Platform Module) attestation.
Dan Lorenc is CEO and co-founder of Chainguard. Beforehand he was staff members software package engineer and direct for Google’s Open Resource Protection Group (GOSST). He has established jobs like Minikube, Skaffold, TektonCD, and Sigstore.
—
New Tech Discussion board gives a venue to take a look at and discuss rising business technological know-how in unparalleled depth and breadth. The collection is subjective, based on our select of the systems we consider to be significant and of greatest interest to InfoWorld readers. InfoWorld does not acknowledge promoting collateral for publication and reserves the proper to edit all contributed written content. Deliver all inquiries to [email protected].
Copyright © 2022 IDG Communications, Inc.